(Washington) Chinese hackers have hacked an American bypass software (VPN) company into the computer networks of US defense companies, IT security consultant Mandient said on Tuesday.
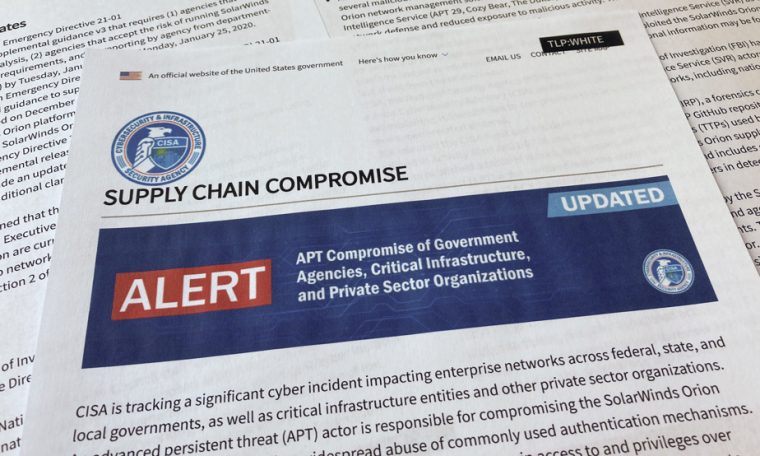
According to the report published by Mandiant, at least two hacker groups, one of which is believed to be close to the Chinese government, are linked to malware exploiting vulnerabilities in VPNs – systems that allow you to establish a secure connection – The company Pulse Secure, which belongs to the Ivanti Group based in Utah, western United States.
The report said the hackers used malware to steal the identity of VPN users and to break into the computer systems of advocacy groups between October 2020 and March 2021.
Governments and financial companies have also been targeted in Europe and the United States, according to the US advisor, which refers to one of the groups as UNC2630.
“We suspect that UNC2630 is operating on behalf of the Chinese government and linked to APT5,” said a hacker group associated with Beijing officials.
The advisor specifies that “trusted third parties” have also linked this new piracy to APT5.
“APT5 regularly targets a network of high-value added groups,” he says. “His favorite targets are aerospace and defense companies based in the United States, Europe and Asia. ”
The report did not specify how many companies were affected.
Pulse Secure mostly confirmed the reports of the mandate, noting that it has already provided solutions to its customers to block the malware.
The VPN creator assured that the hack “affected a limited number of customers.”

“Social media trailblazer. Music junkie. Evil student. Introvert. Typical beer fan. Extreme web ninja. Tv fanatic. Total travel evangelist. Zombie guru.”