Current and former senior managers of SolarWinds are accusing the company of serious mistakes in password security. The problematic password “Solarwinds123” was discovered on the public internet in 2019 by an independent security researcher who warned the company, the leak of the password exposed SolarWinds. ‘ file server.On Friday, during a joint hearing between the House Oversight Committee and the Homeland Security Committee, several US lawmakers fired on SolarWind over the password issue.
“I have a stronger password than aolarwinds123 to block my children.”ipadWatch YouTube too much, “said Rep. Katie Porter.” But you and your company were to stop the Russians from reading the Ministry of Defense emails! “
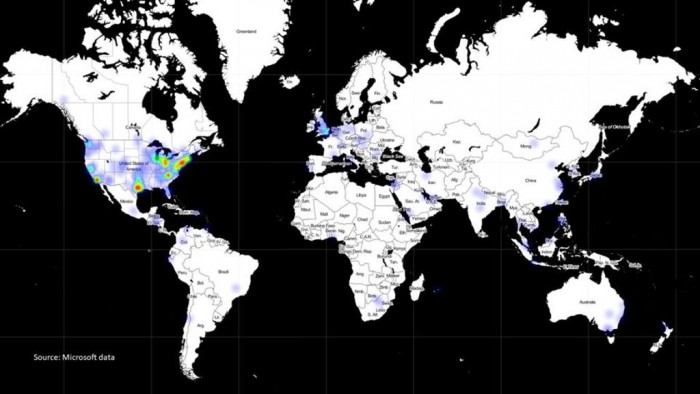
Microsoft President Brad Smith also testified at Friday’s hearing. He later stated that there was no evidence that the Pentagon was indeed influenced by Russian espionage. Microsoft is one of the companies leading the forensic investigation of hacking activities. Microsoft told lawmakers that there is “substantial evidence” that Russia is behind the destructive hackers.
Representatives of SolarWinds told MPs on Friday that once the password problem arose, it was fixed within a few days.
But it is still unclear whether leaked passwords (if any) may have a role in allowing suspected Russian hackers to monitor multiple federal agencies and companies in one of the most serious security breaches in US history. The stolen credentials are one of three possible attack vectors SolarWinds is investigating as it tries to figure out how it was first hacked. Hackers keep hiding malicious code in software updates. SolarWinds then pushed around 18,000 customers, including several federal ones. Agencies.
Sudhakar Ramakrishna, CEO of SolarWinds, said that other theories exploring solar winds include crude guessing the company’s passwords and the possibility of hackers entering through compromised third-party software.
Former SolarWinds CEO Kevin Thompson faced the question of Rep. Rashida Talib, saying that the password issue was “a mistake made by an intern.” “They violated our password policy. They posted this password internally and on their personal Github account. It was discovered and brought to the attention of my security team, and they took it down.” Neither Thompson and Ramakrishna explained to lawmakers why the company has technology. Permitted to use such password at first. Ramakrishna later testified that the password was used in early 2017.
“I believe it was a password used by an intern on one of their Github servers in 2017. It was communicated to our security and removed immediately.”
However, this time period is much longer than the reported time. Researcher Vinoth Kumar, who discovered the leaked password, earlier told CNN that the password would be available online from at least June 2018 until the company fixed the problem in November 2019.
An email between Kumar and Solarwind revealed that the leaked password allowed him to log into the company’s server and successfully save the file. Kumar warned that by using this strategy, any hacker could upload malicious programs to SolarWinds.
At the hearing, FireEye CEO Kevin Mandia said it may not be possible to fully determine how much damage the suspected Russian hacker has caused. We can never know the scope and extent of the damage and can never know how the stolen information benefits the opponent. ”
To assess the damage, authorities should not only list the data accessed, but also envision all the ways that it can be used and misused by foreign actors. This is a difficult task.

“Social media trailblazer. Music junkie. Evil student. Introvert. Typical beer fan. Extreme web ninja. Tv fanatic. Total travel evangelist. Zombie guru.”