This story was originally released and very last current .
Android could have started out with the mantra that builders are permitted to do just about anything as lengthy as they can code it, but factors have modified over the several years as safety and privateness grew to become higher priorities. Every major update in excess of the past ten years has shuttered characteristics or added constraints in the identify of safeguarding consumers, but some sacrifices could not have been solely essential. One more Android 11 trade-off has emerged, this time taking absent the skill for end users to pick 3rd-occasion camera applications to choose photos or films on behalf of other applications, forcing buyers to count only on the built-in camera application.
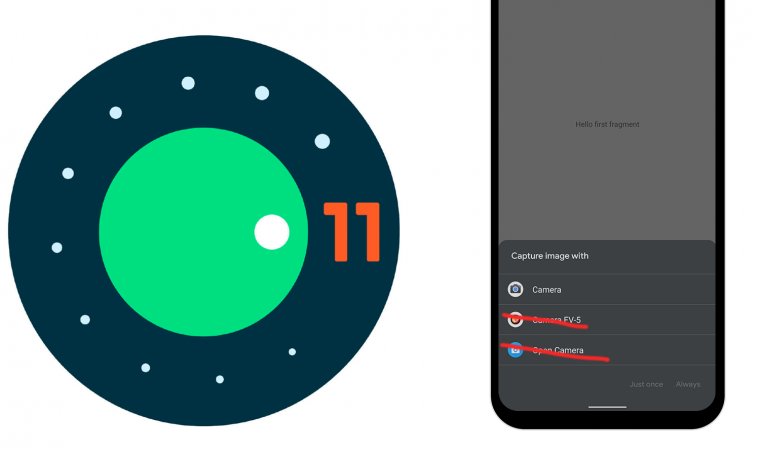
At the heart of this improve is just one of the defining features of Android: the Intent procedure. Let us say you want to get a image of a novelty coffee mug to provide through an auction app. Considering the fact that the auction app was not designed for photography, the developer selected to depart that up to a correct digital camera application. This where the Intent program arrives into participate in. Developers merely build a ask for with a couple requirements and Android will prompt end users to choose from a listing of set up apps to do the task.
Camera picker on Android 10.
Having said that, items are likely to change with Android 11 for apps that ask for pics or movies. 3 distinct intents will cease to work like they used to, including: Video_Seize, Picture_Seize, and Picture_Seize_Protected. Android 11 will now routinely offer the pre-set up camera app to carry out these actions devoid of at any time searching for other applications to fill the function.
Starting off in Android 11, only pre-set up program digicam apps can react to the pursuing intent steps:
If a lot more than one particular pre-installed procedure digital camera app is accessible, the method provides a dialog for the user to pick out an app. If you want your app to use a precise third-party digicam app to capture visuals or movies on its behalf, you can make these intents explicit by setting a package name or ingredient for the intent.
Google describes the modify in a list of new behaviors in Android 11, and more verified it in the Challenge Tracker. Privacy and protection are cited as the purpose, but there’s no discussion about what just built individuals intents dangerous. Perhaps some buyers have been tricked into placing a destructive digicam app as the default and then using it to seize points that ought to have remained personal.
“… we imagine it truly is the correct trade-off to shield the privateness and stability of our end users.” — Google Concern Tracker.
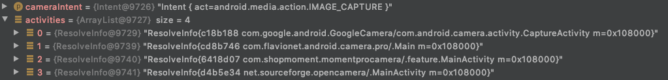
Not only does Android 11 get the liberty of immediately launching the pre-installed digital camera app when asked for, it also helps prevent app developers from conveniently providing their very own interface to simulate the identical performance. I ran a examination with some easy code to query for the digital camera applications on a cellular phone, then ran it on gadgets operating Android 10 and 11 with the exact same set of camera applications put in. Android 10 gave back again a entire established of applications, but Android 11 documented absolutely nothing, not even Google’s individual pre-mounted Camera application.
Earlier mentioned: Debugger watch on Android 10. Beneath: Exact view on Android 11.
As Mark Murphy of CommonsWare details out, Google does prescribe a workaround for builders, while it is not pretty valuable. The documentation advises explicitly examining for mounted digital camera apps by their package deal names — meaning developers would have to decide on preferred apps up front — and sending consumers to individuals applications instantly. Of training course, there are other techniques to get selections with out identifying all package names, like acquiring a record of all apps and then manually looking for intent filters, but this appears to be like an around-complication.
The new conduct is enforced in at the very least the current Android 11 beta launch, and it will transpire to any applications irrespective of no matter if they focus on API 30 or a thing reduce. We will not know nevertheless if the Android CTS (Compatibility Examination Suite) will demand this conduct or if OEMs will be permitted to change it again to the prior procedures, but it really is probably this will develop into the common likely forward.
This unquestionably isn’t really a devastating improve, and for many people that already default to their crafted-in digicam, it will be totally clear. And most applications will still permit people to switch more than to their most popular digicam to get a good shot, then add it from the gallery. Nevertheless, this usually means much more operate for users, and it is a kick in the pants to men and women that regularly snap profile photographs with a filter or for those people that rely on G Cam ports to change their inventory camera. Additionally, some applications don’t enable for distinct workflows, this means you might be trapped with whichever digicam application is there.
Google attributes the modify to possible geotag hijacking
In a response to The Verge, Google discussed that this alter was manufactured to “continue to keep lousy actors from most likely harvesting your location.” This rationalization was also added in an update to the listing of changes in Android 11, along with extra technological facts and a clarification that this does not inhibit the means to set up and use third-get together camera apps.
This is created to assure that the EXIF site metadata is appropriately processed dependent on the spot permissions defined inside of the application sending the intent.
To obtain EXIF locale metadata from the pre-put in procedure digital camera application when utilizing intents that have a person of the preceding intent steps, your app must declare
Access_MEDIA_Sitein addition to theAccessibility_COARSE_LocationorEntry_High-quality_Spotpermission.If you want a unique 3rd-celebration digital camera app to cope with your app’s intent, you could do so by explicitly specifying the third-bash camera app’s package title to satisfy the intent.
This change does not have an effect on users’ ability to install and use any digital camera application to capture photographs or movies instantly. A consumer can set a third celebration camera application as the default digital camera app. This transform also isn’t going to have an affect on intent steps that launch the user-specified default digital camera application, including
android.company.MediaStore.INTENT_Motion_Continue to_Graphic_Digicam,android.service provider.MediaStore.INTENT_Action_Even now_Graphic_Digital camera_Secure, orandroid.service provider.MediaStore.INTENT_Action_Online video_Digicam.
Harvesting EXIF info in this way has in fact been documented in the previous when Shutterfly was caught carrying out it in 2019. This alter will prohibit the least difficult route to hijacking locale info, but it leaves some workarounds like contacting out to digital camera applications specifically or inquiring buyers to consider images and load them from a media company. It truly is possible Google could have to just take further methods to completely shut the door on this tactic.